Introduction
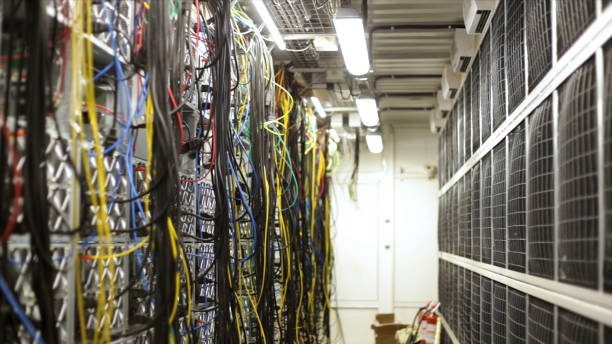
If you’re hosting your website on a virtual private server (VPS), you’ve probably already secured it against common attacks, like bots crawling your site or hackers trying to guess which account names and passwords are in use. But there are still more ways that attackers can try to break into your server. The best way to protect against these threats is to use a firewall—a system designed specifically for preventing attacks on servers by filtering traffic before it reaches its destination. And as we’ll see later in this article, installing a firewall is pretty easy!
Lock Down SSH
To lock down SSH, we need to take a few steps. First and foremost, we’ll install fail2ban. This is a service that monitors for suspicious logins and blocks them after a certain number of incorrect attempts. We’ll also restrict SSH access only to specific IP addresses and use public key authentication instead of passwords whenever possible (this will make it much more difficult for attackers who may have stolen your password).
Scan for Malware
To scan for malware, you should first run a malware scanner on your files, databases and server. Make sure to also scan any other files that could be affected, such as backups and email.
Install SSL
Before you can get started, you need to purchase a certificate through a trusted provider. The best way to do this is by talking to your web hosting company. They should be able to give you some recommendations for providers and also make sure that the certificate can be installed correctly on your VPS.
Secure the Web Server
To secure your web server, you must take several steps:
- Install a firewall. This is one of the most important steps to securing your virtual private server (VPS). A firewall blocks access to ports that you don’t need, as well as IP addresses that you don’t need. You should also block IP addresses that are not from your network.
- Use the correct port for Apache or Nginx on your VPS and make sure it’s closed off from any other ports in use by other applications or services on the same machine, such as MySQL and SSH.
Disable Password Authentication for SSH
Password authentication is a security risk, as it is vulnerable to brute-force attacks. You should disable password authentication and use keys instead. If you are using SSH agent forwarding, you can use public key authentication for added security.
Conclusion
We hope this article has given you some insight into how to secure your VPS. While there are many different ways to go about it, we believe that these are some of the most important steps you can take to ensure that your website is safe from intruders and hackers.