DNS Propagation and How it Works?

Reading Time: 2 minutes Introduction Understanding the ins and outs of DNS propagation is crucial for anyone managing a website or domain. In this comprehensive guide, we’ll break down the complexities of DNS propagation, explaining the process step by step. Whether you’re a seasoned webmaster or a newcomer to the online realm, this article will equip you with the […]
What Is WordPress

Reading Time: 2 minutes Have you ever wondered, “What Is WordPress?” If you’re entering the world of website creation, you’ve likely come across this powerful tool. WordPress, a content management system (CMS), has transformed the way individuals, businesses, and developers manage and create websites. In this exploration, we’ll delve into the basics of WordPress, explore its user-friendly features, and […]
Recover Joomla Admin Password

Reading Time: 2 minutes Recover Joomla Admin Password. Securing access to your Joomla admin panel is crucial for maintaining control over your website. In this comprehensive guide, we’ll walk you through the process of recovering your Joomla admin password. Whether you’ve forgotten your password or encountered login issues, these steps will help you regain control swiftly. Recover Joomla Admin […]
SEO For Church Websites
Reading Time: 2 minutes In the digital age, where the internet is the first place people turn to for information, ensuring that your church’s online presence is optimized is crucial. Search Engine Optimization (SEO) for church websites can be a powerful tool to connect with both existing and potential members, and spread the message of faith far and wide. […]
Install ClamAV on cPanel

Reading Time: 2 minutes When it comes to ensuring the security of your cPanel server, installing ClamAV is a crucial step in safeguarding against trojans, viruses, and various types of malware. In this guide, we’ll walk you through the process of installing ClamAV on your cPanel server, enhancing your server’s defenses against potential threats. This step-by-step tutorial provides a […]
cPanel Log Locations
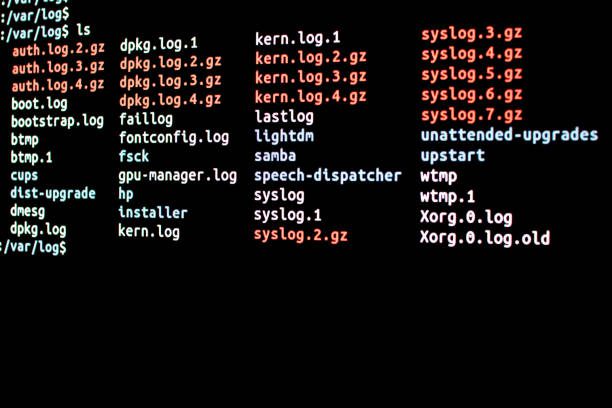
Reading Time: 2 minutes In the dynamic landscape of web hosting and server management, understanding cPanel log locations is paramount for ensuring optimal performance, security, and troubleshooting capabilities. As website administrators and developers delve into the intricacies of cPanel, familiarizing themselves with the precise locations of log files becomes a key skill. In this comprehensive guide, we will unravel […]
How to Show Hidden Files in cPanel

Reading Time: 2 minutes Ever wondered how to show hidden files in cPanel and unlock the full potential of your website? You’re not alone. Delve beyond the surface, where hidden files orchestrate the digital symphony of your online presence. In this blog post, we’ll guide you through cPanel, unveiling the secrets of these hidden treasures and empowering you to […]
Benefits of Using Website Hosting?
Reading Time: 2 minutes The Power of Website Hosting: Unleash Your Digital Potential In today’s digital age, a website is often the first point of contact between your business and potential customers. But have you ever thought about what lies behind the scenes, making your website accessible, secure, and reliable? The answer is website hosting, and in this article, […]
How Many Website Are There on The Internet?

Reading Time: 2 minutes Introduction Have you ever pondered the vastness of the internet? In a world where digital connectivity is an integral part of our lives, one question looms large: How Many Websites Are There on The Internet? In this article, we will embark on a fascinating journey to uncover the answer while navigating the boundless expanses of […]
Safeguarding Your Website: Fusion Arc Hosting’s Multi-Layered Security Measures against Cyber Attacks
Reading Time: 2 minutes Understanding the Threat Landscape In today’s fast-paced digital world, cyber attacks pose a constant threat to online assets. At Fusion Arc Hosting, we understand the importance of staying ahead of the ever-evolving threat landscape. With malicious actors continuously seeking vulnerabilities, Brute Force Attacks and DDoS attacks remain among the most common and disruptive methods employed. […]